Security “without protection” by data nullification:
as information leaks no longer need to be prevented
with a new concept without applying
the traditional encryption method
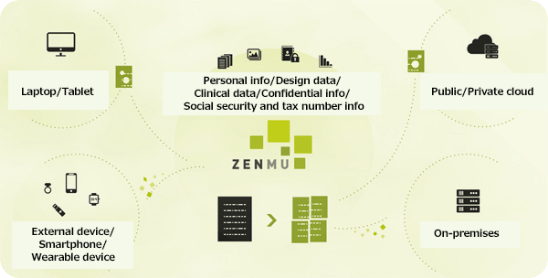
by storing split data across various locations

FUTURE
Trust from stakeholders ensured
ZENMU, which nullifies data, solves various problems related to information leaks. Stakeholders can be given much greater peace of mind through implementation of robust security countermeasures for personal information and confidential matters, measures for dealing with confidential matters, and reduction of risk from human error, etc. Company security policies can even be changed by using ZENMU.


without users being conscious of it
Information safety established without users being conscious of it
We are living in a time when greater attention is given to data protection issues such as acquisition/management of all kinds of customer information and support for big data generated in the IoT area, which is expected to undergo even greater expansion in the future. In terms of information security countermeasures, nullifying the data itself will result in no need for network security to prevent leakage, hacking and tampering.
Released from cost of new security measures
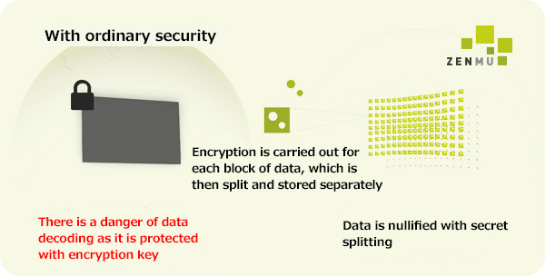
Security countermeasures based on encryption alone are theoretically at risk of being decoded. Also, with security countermeasures based on “protection”, the same processes have been repeated over and again as countermeasures are carried out every time a new problem arises. ZENMU implements “security without the need for protection” by nullifying the data itself.


TECHNOLOGY
Secret Splitting technology
Splitting
technology




 CONTACT NOW
CONTACT NOW